 CacheGuard-OS
CacheGuard-OSUser's Guide - Version UF-2.5.2
URL Guarding
URL guarding (or filtering) allows you to control Web browsing within your organisation. You can activate URL guarding using the mode guard on command. This feature is based on blacklists (denied) and whitelists (allowed) of domain names and URLs that can be managed using the urllist command. You also have the possibility to use regular expressions in addition to URL lists. In this way, you can either permit access only to websites included in your whitelists or block access to URLs appearing in your blacklists. The guard command allows you to configure URL guarding by creating filters, policies, and rules.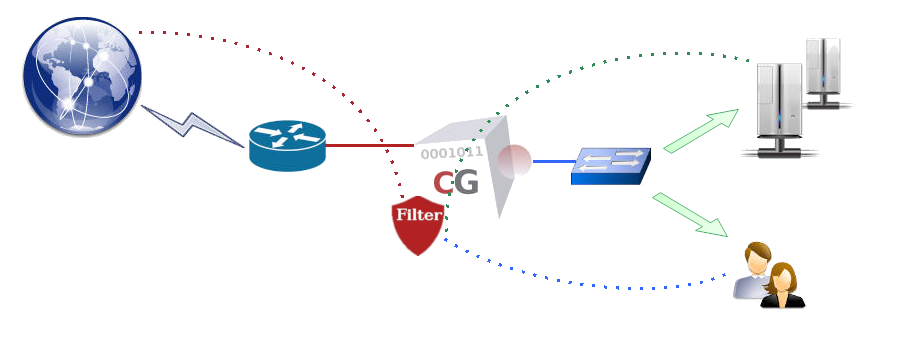
- mode guard on
- urllist add Advertising
- urllist add Malware
- urllist load create Advertising tftp 172.18.2.1 Advertising domains urls
- urllist load create Malware tftp 172.18.2.1 Malware domains urls
- guard rule add default deny Advertising Malware
- apply
Domain name files (.domains.gz) must contain a list of domain base names (one per line). A domain base name is a domain name without any prefix. For instance, example.com is considered a domain base name, whereas www.example.com is not. To specify a domain name with a prefix, you should include it in a URL file (.urls.gz). URL files (.urls.gz) must contain a list of content specifications (one per line) similar to a URL without the protocol part, in the form <domain-name>/<path>, where <domain-name> is a fully qualified domain name and <path> is a path specification. For example, www.example.com/foo/bar/zoo.html is a valid URL in this context, while http://www.example.com:81/foo/bar/zoo.html?id=1 is not.
URL Lists
URL guarding is primarily based on URL lists that should be kept updated, as thousands of new websites appear on the Web every day. Daily updated URL lists are offered as an optional service by CacheGuard Technologies, which you can easily subscribe to. However, you also have the option to use your own URL lists and keep them automatically updated on your CacheGuard appliance. To update a URL list, you can either recreate it entirely by loading its full content from a URL list file or simply load a difference file (preferred method). For example, to automatically update the URL list named WebMail from ftp://172.18.2.1/DF/WebMail on a daily basis, use the following commands:- password file add ftp 172.18.2.1 john
- urllist auto WebMail on load update daily ftp 172.18.2.1 DF/WebMail
- apply
Policies & Filters
Guard policies allow you to apply URL guarding to specific groups of Web clients matching certain criteria. For instance, you may wish to block Advertising websites for users in the 10.0.10.0 255.255.255.0 network who belong to the LDAP group cn=support,ou=groups,dc=example,dc=com between 12:30 and 13:30 (1:30 PM). To achieve this, you must first create three guard filters, then associate them with a policy, and finally create a guard rule based on that policy. The following commands define such a guarding policy:- guard filter ip add london network 10.0.10.0 255.255.255.0
- guard filter time add lunchHours slot 12:30-13:30
- guard filter ldap add supportTeam 'cn=support,ou=groups,dc=example,dc=com' memberUid 'objectclass=posixGroup'
- guard policy add londonSupport ip london time lunchHours ldap supportTeam
- guard rule add londonSupport deny Advertising
- apply